Table of contents of the article:
The climate is not calm and the current news that has just arrived regarding the Ukraine - Russia conflict which saw the invasion of Ukraine by the Russian army on the orders of President Putin, does not seem to reassure that there may be a term of the conflict soon. Rumors of economic and military support from NATO states with particular US involvement (Biden has already allocated a very first trance of 600 million dollars in arms for Ukraine in the immediate future), suggests that the affair could have escalated of violence with only 2 historical precedents, leading in fact to a real third world war.
This eventuality, which at first seemed absolutely unlikely, instead begins to take on the appearance of an eventuality that should not be underestimated and to begin to consciously evaluate.
Regardless of the economic and commercial relations with Russia that Italy has always supported, one cannot fail to keep in mind the obligations and duties that Italy owes to member states as a member and signatory of NATO agreements.
By virtue of this as has happened in other Middle Eastern conflicts in the vicinity of the events of 11 September, Ad perpetuam rei memoriam, it is mathematically certain that if Russia's current act of force is opposed by NATO, member states in unison must provide at least AS MINIMUM logistical, financial, as well as territorial support in support of NATO and the warfare to come.
Assuming that we are limited to giving only support and not participating militarily in war actions that would make everything even more risky.
Having made the necessary premises and the ever-changing scenario being still indeterminable for now, we need to focus, at least for what concerns us from a professional point of view, to evaluate the room for maneuver for what could affect a cybernetic war or Cyber War between NATO countries. and Russia, or to begin to understand how to secure companies by re-evaluating some choices made in the past in which Italy / Russia relations were not as critical as they are currently (although Italy's moderation has now been demonstrated).
Uninstall Kaspersky Antivirus and related software solutions under their brand from all company workstations.
La Kaspersky Lab ZAO (Лаборатория Касперского), better known as Kaspersky, is a Russian company based in Moscow founded in 1997 by Yevgeny Kaspersky and specializes in the production of software designed for IT security; Kaspersky Lab (/ kæˈspɜːrski /; Russian: Лаборатория Касперского, Laboratoriya Kasperskogo) is a multinational cybersecurity and antivirus provider based in Moscow, Russia, and operated by a UK holding company. Kaspersky Lab develops and sells antivirus, Internet security, password management, endpoint security and other cybersecurity products and services

On October 6, 2017, the Wall Street Journal - citing "more people aware of the matter" - said that in 2015 hackers working for the Russian government used Kaspersky antivirus software to steal classified material from a home computer belonging to a National Security Agency (NSA) contractor. According to the report, the incident occurred in 2015 and remained unknown until early 2016. Reportedly, (here link them) the stolen material included "details on how the NSA penetrates foreign computer networks, the computer code it uses for such espionage, and how it defends networks within the United States" [14] The New York Times reported that the hacks they had been discovered by Israeli intelligence agents who had hacked into Kaspersky's network. On October 11, 2017, the Wall Street Journal further claimed that Russian intelligence uses Kaspersky software to scan computers around the world for material of interest. The company once again denied the reports, claiming they were "groundless paranoia" and a "witch hunt," and suspected that major US media simultaneously "were latching on to us almost in full force and fantasizing simultaneously, since if they get an order, but they are confused in the details. "
Kaspersky, therefore, following these controversies over the accusations of having engaged with the Russian Federal Security Service (FSB), has suffered obvious consequences:The United States Department of Homeland Security banned Kaspersky products from all government departments on September 13, 2017. In October 2017, subsequent reports claimed that hackers working for the Russian government stole confidential data from the Russian government's home computer. a US National Security Agency contractor using Kaspersky antivirus software . Kaspersky denied the allegations, reporting that the software had detected Equation Group malware samples that it uploaded to its servers for analysis during its normal operation. The company has since announced commitments to increased responsibility, such as soliciting independent reviews and source code verification of its software, and announcing that it would migrate some of its core infrastructure for foreign customers from Russia to Switzerland. In recent years, Kaspersky has received several allegations of collaboration with the Russian Federal Security Service (FSB), allegations that the company has consistently rejected by soliciting independent reviews and source code verifications of its software and announcing the move to Switzerland of part of its infrastructure. software assembly.
On November 13, 2017, the British intelligence agency MI6 raised suspicions about Kaspersky Lab software after it was distributed free to over 2 million customers Barclays in the UK. On December 2, 2017, Barclay's announced that it would no longer provide new customers with the company's software. Also around 2 December 2017, the National Cyber Security Center British advised, as a national security precaution, that UK government departments avoided Russia-based antivirus software such as Kaspersky. On December 9, 2017, the US government banned Kaspersky from federal civilian and military computers as part of a broader defense bill.

Less than a week ago, on February 22nd Umberto Rapetto - Italian general of the Guardia di Finanza, on leave since 2012 and founder of Gate (Telematic anti-crime group), which later became the Special Telematic Fraud Unit - revealed in the article on Infosec.news https://www.infosec.news/2022/02/22/editoriale/in-tempi-di-guerra-la-nostra-difesa-ha-ancora-un-antivirus-russo/ his perplexity about the use of a "famous Russian antivirus" by the Italian government authorities.
It is worth mentioning an important passage from the article on Infosec.news:
Peering on the web we learn, in fact, that our Ministry of Defense would have been for years a valuable customer of a particularly well-established software house, whose indisputable technological capabilities have always been accompanied by some suspicion of possibly understandable proximity to the country of origin.
In 2018, the story of the ministries and public bodies that had bought the programs for the protection of their information systems from the Russian company Kaspersky came out. The company created, owned and directed by a great professional who graduated in Moscow in 1987 at the Faculty of Mathematics of the KGB High School boasted as clients the departments of Cultural Activities and Tourism, Defense, Justice, Infrastructure, Economy, Interior, Education, Development Economic, Agcom (the Competition and Market Authority), ENAV, CNR and the Central Directorate of Electoral Services ...
The request for "civic access" (taking advantage of the possibilities opened up by the so-called Italian Freedom of Information Act, which entered into force in December 2016) formulated by Euronews and the Hermes Center for Transparency and Digital Rights led to the drafting of an explanatory table that did not it has only administrative value but which can lead to reflections of a strategic nature.
Probably the repetition of a similar response - extended to all supplies whose "flag" origin could cause concern - would be a valid opportunity to detect potential risks and to adopt some late initiative in the best tradition that wants to close the stalls after the oxen have fled.
Having therefore necessarily to take into consideration the above premises, it appears peaceful and evident in compliance with the precautionary principle (and therefore only for precautionary purposes in the absence of direct accusations and specific evidence), avoid purchasing Kaspersky branded solutions and immediately replace them with alternative software such as Avira, BitDefender, GData or NOD32, respectively German, Romanian and Slovak solutions, of which we recommend the excellent BitDefender according to the statistics and data of independent laboratories.

Someone will read with extreme amazement that there have not been cited brands of excellence and noble as McAfee, Norton, Checkpoint.
It is not an oversight, but the wise choice of choose only and exclusively European software products and not controlled by foreign holding companies and / or at least non-EU interests.
Although there is no regulation on this nor any obligation in what is the regulation of the European Union better known as GDPR it is always recommended to use where possible and replaceable European production software. This should be the practice for what concerns government and ministerial offices and instead unfortunately there is still a legislative hole in this regard that we hope will be filled following current events.
Filtering connections from Russia at the network and application level
Although this operation can be postponed to a more critical diplomatic situation, it is already necessary to take into account the need to filter the connections (and any attack attempts by Russian IPs).
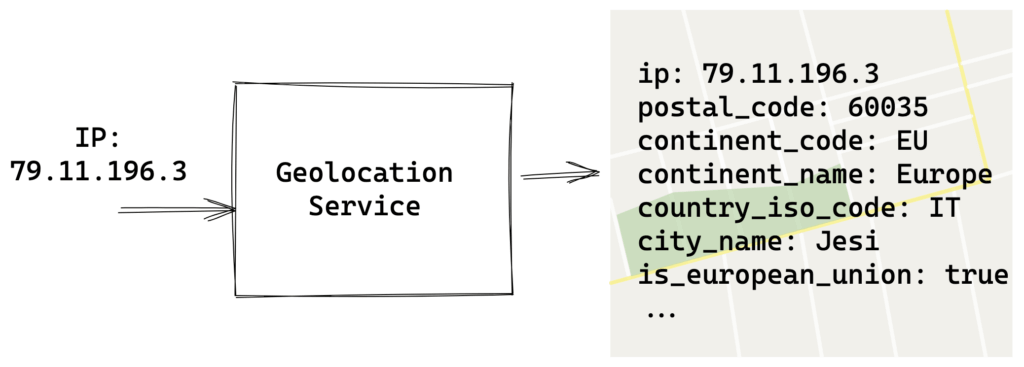
All this can be done by the company CTO who will draw up a plan with related technologies to provide for the filtering of Russian connections, relying on Geo IP Geolocation (through, for example, MaxMind technology) which allows you to trace the origin of a IP network connection
For those who want a more streamlined approach at the SOHO (Small Office Home Office) level, you can opt for Free solutions such as CloudFlare filtering.
It would be useful, for example, to block requests from Russia with a CAPTHCA (or completely block for Italian institutional and government sites).
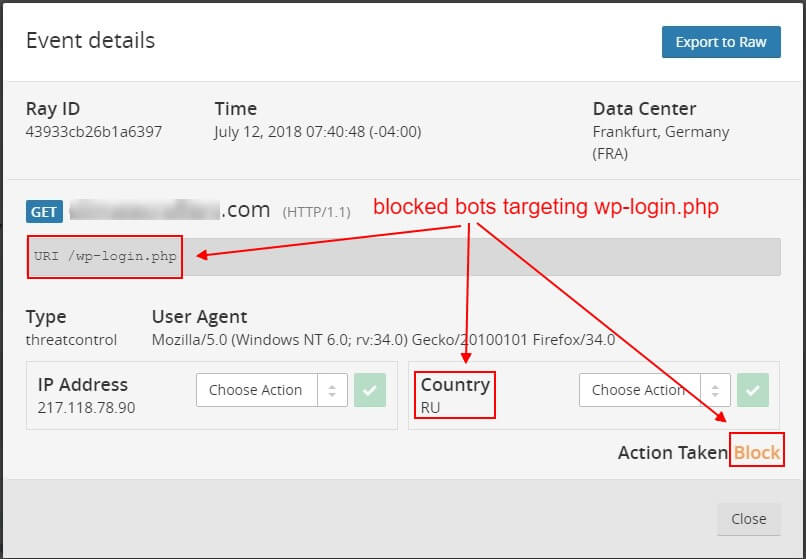
We have talked about CloudFlare in depth in this article DDOS attacks and extortion of payments in Bitcoin? How to protect yourself with CloudFlare and today it is the fastest and most immediate solution to implement at low cost (if you are familiar practically for free) an important filtering system of incoming connections.
Use NGINX Web Server only from the version after the acquisition of F5

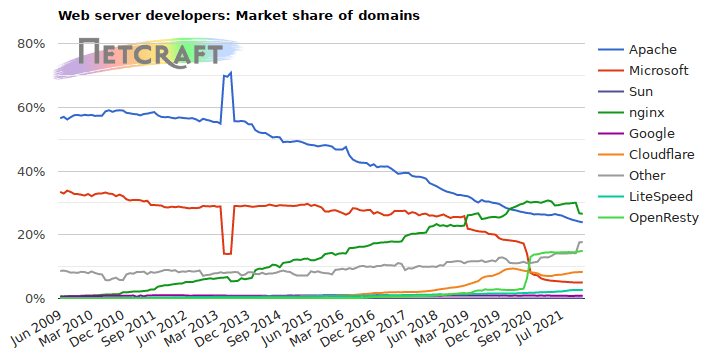
NGINX Inc is the support and consulting arm of a open source reverse proxy web server (Reverse Proxy) which is very popular with some of the loudest internet services on the planet. The company is of Russian origin but was sold to F5 Networks in 2019 . The founder of the company, Igor Sysoev, announced his departure in January this year.
Considering the growing trend of NGINX Webserver (which is for example at the heart of our high performance Hosting infrastructure), it would be advisable to update NGINX to the latest version, (or in any case recent at least by 2021) possibly opting for recompilation from source, rather than from binary packages from repositories like yum or apt.
It is worth mentioning the strange case of the Russian police raiding the NGINX offices in Moscow in order to be able to make some considerations regarding the risk that was run until NGINX was acquired by the US company F5 for about 600 million dollars. .
On December 12, 2019, Russian police broke into Nginx's Moscow office, arrested company employees, original developer Igor Sysoev, and another co-founder Maxim Konovalov.
The searches are due to complaints filed by Rambler Group against NGINX. Rambler claims that Sysoev developed the open source Nginx web server when working as a system administrator in Rambler.
The Nginx web server it was publicly released in the year 2004, it is free open source software and can also be used as a reverse proxy or load balancer.
Igor Sysoev claimed to have developed Nginx "with the aim of overcoming some barriers of scaling the difficulties of the web infrastructure in managing many simultaneous connections, reducing latency and downloading static content, SSL and persistent connections".
Nginx, Inc was formed in the year 2011 with the aim of providing support and providing Nginx plus paid software. In 2019 NGINX was acquired by F5 Networks for $ 670 million. According to the w3techs report, Nginx is used by over 30% of websites, including Gainst like Facebook, Netflix and Apple.
The Rambler group claimed that Igor Sysoev started the development of NGINX when he was an employee of the Rambler Internet Holding company; so, "therefore any use of this program without the consent of the Rambler Group is a violation of the exclusive right".
Igor Sysoev stated in an interview with Hacker magazine in 2012 that he developed NGINX in his spare time while working at Rambler, he also said that "programming was not part of my job responsibilities at Rambler".
Rambler also claimed that Sysoev worked on the Nginx project during working hours; then, he distributed the web server software for free on the Internet, later the property rights of Nginx Inc. Rambler said this deal and free distribution are illegal and cost an estimated damage of 51,4 million rubles ($ 820.000 ).
According to the relationship of Forbes, the case went bankrupt under article 146, part 3, leading to 6 years of imprisonment, with fines of up to 500.000 rubles.
Backup and Disaster Recovery
Although it must already be a tested and consolidated practice also on the basis of the directives in force and the former DPS (Programmatic Document on Security) - now abolished - it must always be remembered that a Backup and Disaster Recovery procedure is an added value both for the individual and for the company. Regardless of the size of the company that will use based on the available budget of professionals in the field of data security, we recommend that all companies of any size use at least basic Backup and Disaster recovery solutions and possibly if the connection allows (at least 20 megabits in Upload) to use Cloud solutions rather than physical backups in the company. Better if both with double security copy.
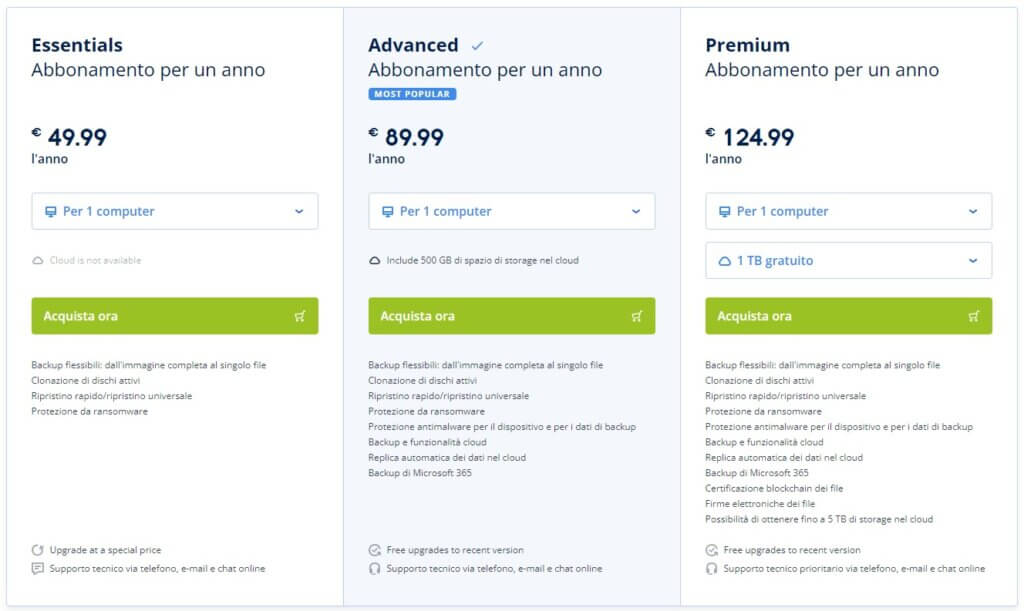
For small and medium-sized companies, a suitable solution could be that of Acronis.
Acronis Inc. is a software company headquartered in Burlington Maryland and several smaller offices in Asia and Europe. The company is known for software systems that enable backup and disaster recovery for both a business and home market.
The strong point is its offer of integrated cyber protection, together with the creation of backup and recovery disk images, partition and management, boot and management, data migration and entire systems, data deduplication. It also develops virtualization software with the purpose of migrating a physical server to a virtual server (such as VMware), or what is also called P2V. Its best known product is Acronis True Image, which allows you to create an image of a computer that can be reinstalled on the same or another machine.
Acronis provides "turnkey" solutions for companies of any size and any budget (starting from 90 € / year for Cloud solutions) and unlike other cutting-edge products such as VEAM for example, it does not need to have other interlocutors and suppliers to remote cloud storage management. It is therefore suitable for small / medium-sized companies that want to have a solution that is now the market leader, quick, fast, balancing a low cost with a high added value.
Good advice but not only in times of war.
These are the basic tips that every company should take into consideration in view of possible attacks, and not necessarily attacks derived from the current war climate, but from those that arrive every day on the connection of your company and your site without them. give the slightest account.
How many cyber security attacks are there every day?
A Clark School study at the University of Maryland found that 2,244 attacks occurred every day which is almost 1 cyber attack every 39 seconds.
A study by the Australian Government's Australian Cyber Security Center (ACSC) found that an average of 164 cybercrimes per day or about one every 10 minutes.
What is the most alarming security problem on the internet today?
Ransomware is the number one cybersecurity threat of 2021. Ransomware is one of the most dangerous types of hacks because it is relatively easy and cheap to perform and because it gives cybercriminals the ability to deny access to computer files until no ransom is paid.
How many cyber attacks happened in 2020?
An Arkose Labs study estimated that by August 2020 there had been around 445 million cyber attacks in 2020 globally, double that of all of 2019. Cybercrime is reaching an all-time high and there will be nearly a billion attacks on a global scale this year.
Where do most cyber attacks come from?
Russia, Brazil and China are the top three countries where cyber attacks originate.
Russian hackers tend to target banks in the US and Europe. Since the XNUMXth century, the Russian education system has encouraged the pursuit of scientific knowledge and curiosity in its students, which has had the side effect of favoring cybercriminals.
Brazilian hackers typically use simple Russian-inspired tactics that have little exposure risk. Hackers in China send mass text messages in an attempt to coerce victims into fraudulent transfers.
How long does it take for cyber attacks to be detected?
On average, it takes approx 280 days to detect and stop a cyber attack. A typical organization takes approximately 197 days to identify a threat, but some breaches can avoid detection for a long time. How long it takes your business to remove a threat depends on the robustness of your security system.
Once detected, an attack often persists for an average of another 69 days. Companies that can subdue attacks in less time can save hundreds of thousands of dollars in recovery costs.
Russian utility companies will also be affected
Many global technology giants in the software and services industries have used Russian and Eastern European developers in the past due to their high-quality, affordable work compared to their US and Western European-based counterparts. And many have invested hundreds of millions of dollars to have a developer as well as reseller channel presence in Russia.
World governments do not need to impose Iranian-style isolationist sanctions against Russia for a snowball effect to start within US companies using Russian software or services.
Escalating a full-blown conflict in Ukraine will make C-seats within global corporations extremely concerned about the use of software that comes from Russia or was produced by Russian citizens. The more conservative companies are likely to “rip and replace” most of the standard stuff and choose other solutions, preferably American ones.
Russian mobile apps? BYOD mobile device management (MDM) policies will prevent them from being installed on any device that can access a corporate network. And if sanctions are put in place by world governments, we can expect them to disappear completely from mobile device stores.
Countless games and apps from Russia may no longer exist when effective sanctions are implemented on that sector.
But C-seats won't wait for governments to ban Russian software. If there is a lack of confidence in a vendor's reliability, or if you fear that its customers' loyalty may be swapped or influenced by Putin's regime and used to compromise their systems, rest assured that Russian-sourced software will disappear a lot. quickly from the corporate IT infrastructure.
Contractor visas will surely be canceled en masse or not renewed for Russian citizens doing jobs for large corporations. You can count on it.
Any vendor being considered for a large software contract with a US company will undergo a thorough check and will be asked if any of their products involve Russian developers. If it does not pass the most basic audits, they can simply forget about doing business in this country.
So if a vendor has a major Russian developer workforce, they'll have to pack up and move those labs to the US or a country that's better aligned with US interests, as we've seen with the companies listed above. This is especially true for anyone who wants to do federal contract work.
Then there is the issue of custom code produced by outsourced companies. It gets a lot more complicated.
Obviously, there is the question of how recent the code is and whether or not there are adequate methods to verify it. We can expect that soon there will be service products offered by US and Western European IT companies to sift through huge amounts of custom code so that they can be sure that Russian citizens leave no compromises under the influence of the Putin regime.
If you thought your Y2K mitigation was expensive, wait until your company experiences the Russian Purge.
I don't have to tell any of you how expensive this proposal is. The wealthiest companies, sensing a huge risk to customer safety and trust, will address this issue as quickly as possible and swallow the bitter pill of expensive audits.
But many companies may not have the immediate funds to do so. They will do their best to mitigate the risk on their own, and the compromised code could stay around for years until major system migrations occur and the old code is (hopefully) eliminated.
We will almost certainly be dealing with Russian cyber attacks from within the walls of our own companies in the years to come, from software initially developed under the aegis of having access to talented, strategically outsourced, relatively cheap and highly skilled programmers.
Will Russian software and services become the first victim of a digital war?
